Introduction to the concept of Anti-Money Laundering
MOBILE MONEY BANKING:
- Anti-Money Laundering (AML) and dismantling terror financing networks by exclusion from the mobile banking system
- The Alleged Threat of Mobile Money
- An important factor within money is micro-structuring also known as “smurfing”
- Further challenges for law enforcement
- The threats of mobile money
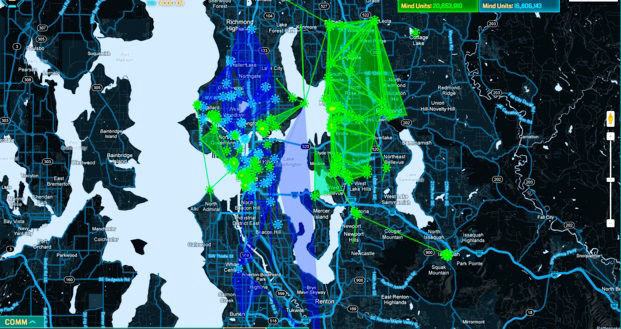
Innovative Technology
ELECTRONIC PAYMENT CARD MONEY LAUNDERING DETECTION SYSTEM FOR ELECTRONIC PAYMENT CARDS
The algorithm example used in this report is also called an exemplary embodiment which is simply put, the preferred example. It is just another terminology for “example” but specifically used when referring to a patent. This Anti Money Laundering, AML, system has been chosen to represent how an AML monitoring system should function.